Office 365. We know what it is. We’ve heard the name and you probably know someone that has migrated from their on-premises Exchange organization to it. And if your company is one of those who has migrated to Office 365, then you are probably aware of the one struggle that everyone who’s ever moved to 365 has had to deal with – saving credentials for Outlook.
Now for those who may be curious about moving to Office 365, you are probably wondering what I’m talking about. To catch you up to speed, when users connect to Office365 via Outlook, they cannot utilize ADFS to do a true Single Sign On (SSO) experience. Instead, Outlook uses the Outlook Anywhere function, and unfortunately, requires the use of Basic Authentication, meaning you must enter in a username and password every time, unless you of course, cache the credentials.
For a long time, most of my clients would ask me “is Microsoft ever going to change this?”, and would state “well this defeats the purpose of utilizing ADFS for true SSO.” And I agree, but now, it seems like Microsoft’s ears were ringing, because the wish of using Outlook with Office 365 and not having to cache credentials has been granted!
But how does this work, and what limitations are there? I’ll explain in this article.
Modern Authentication – What is it?
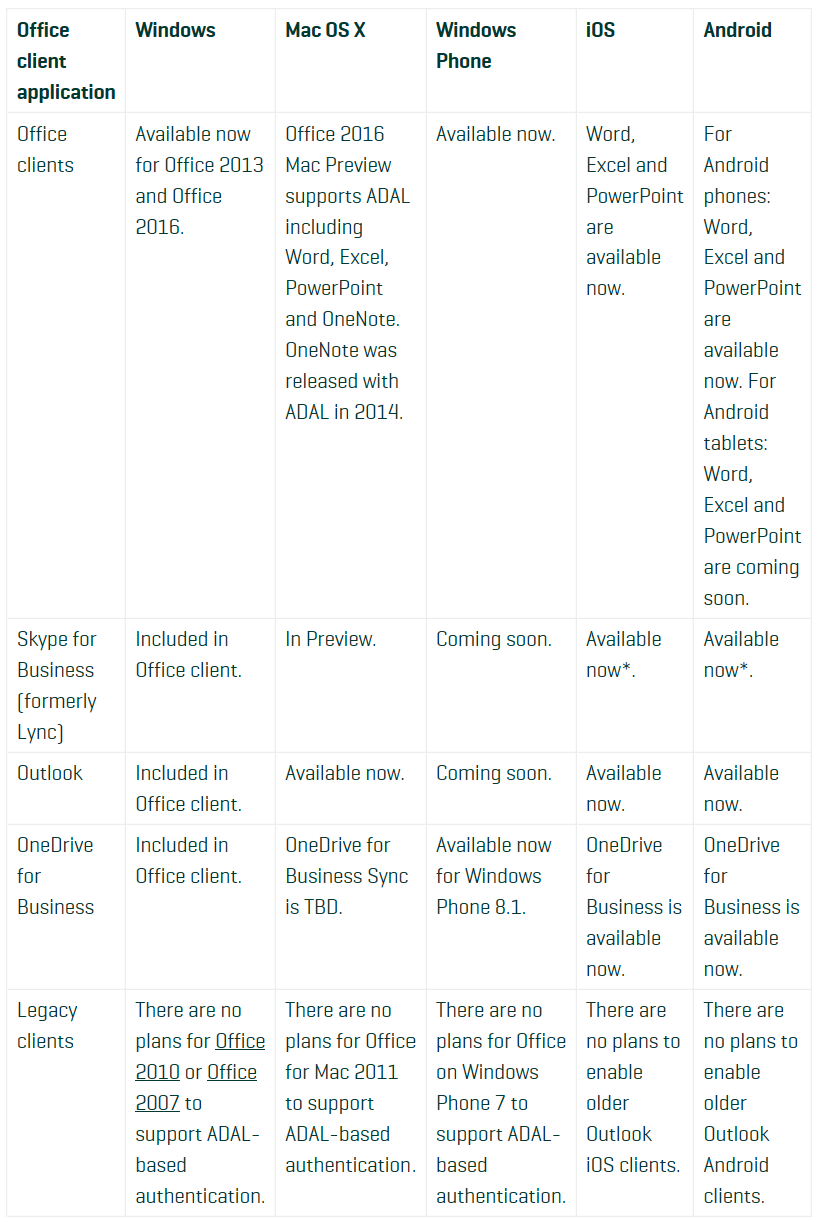
Modern Authentication brings Active Directory Authentication Library (ADAL)-based sign-in to Office client apps across platforms. This enables sign-in features such as Multi-Factor Authentication (MFA), SAML-based third-party Identity Providers with Office client applications, smart card and certificate-based authentication, and it removes the need for Outlook to use the basic authentication protocol. The chart below shows the availability of Modern Authentication across Office apps:
Now, let me take this time to further break down how Modern Authentication works. The Office client will behave exactly as a Web Browser when authenticating, it will send the Access Token requests directly to the authentication provider instead of sending username and password to the resource, and if you are enabled for MFA, you will get the exact same behavior you get when accessing OWA or SharePoint Online; goodbye pop-ups and App Passwords, hello real SSO and MFA!
By default, your Exchange and Skype for Business Online tenants are not enabled for Modern Authentication. You must manually enable it via PowerShell. Modern Authentication support is also not enabled in Office 2013 by default either. You must ensure that the March 2015 update patch is installed prior to enabling this in your tenant. All versions of Office 2016, however, have Modern Authentication support enabled by default, and require no further action once enabled on the Exchange Online and Skype for Business Online tenants.
So what are my benefits from enabling Modern Authentication?
Right out of the gate, the first benefit is new and existing users will no longer need to enter credentials into Office to connect to Office 365. Modern Authentication will use the OATH2 to authenticate to ADFS (via the addition of ADFS into the trusted local intranet sites) on the client’s behalf, and will SSO the user.
This benefit is great for those of you out there who use non-persistent VDI deployments with RDS, Citrix, and VMware. Meaning you can now deploy Volume Licensed copies of Office 2013/2016 or Click-2-Run copies of Office 365 to your VM’s and allow mail profile setups without users having to enter in any credentials.
Another great benefit of this feature is available for IOS and Android devices, which means corporate enrolled devices can have clients such as Skype for Business and Outlook deployed to them, and can be configured to do SSO, SAML, and MFA via Modern Authentication as well.
This is also big news for those who are planning to migrate to Office 365 in the future, as it will now allow you to migrate mailboxes seamlessly, without having to let the end-user know that they may have to enter in credentials once their migration is complete.
So where are my drawbacks?
Naturally, the first question will be “well does this work for Office suites lower than 2013?”. The answer there will be "no." Microsoft has made it clear that they are trying to push past Office suites older than 2013, meaning they are not offering up much support for 2010 and lower. If you would like to utilize Modern Authentication, you’ll need to, at a minimum, upgrade to Office 2013.
Sticking with this subject, Office for Mac 2011, Windows Phone 7, and older versions of Android and IOS clients are not supported either.
Another current drawback is that Modern Authentication for PowerShell is still in Public Preview currently. You can enable this for your tenant, however, there will be very limited support. Also, be aware, that Modern Authentication is only supported with ADFS 3.0, which is only available in Windows Server 2012 R2 and Windows Server 2016. ADFS 2.1 (Windows Server 2012) and ADFS 2.0 (Windows Server 2008/2008 R2) are not supported, which means you will have to upgrade to take advantage of this feature. Also, you must have ADFS 3.0 to even use Modern Authentication. If you are just using Password Synchronization or Cloud Identity as your method of authentication to Office 365, you will not be able to leverage Modern Authentication.
The final drawback can occur only if you plan on using Modern Authentication with third-party identity providers. Currently, all providers listed are qualified by Microsoft for Modern Authentication. However, if your provider is not on this list, you can download a connectivity test tool from https://testconnectivity.microsoft.com/?tabid=Client and see if Modern Authentication will work. If not, you may not be able to use modern authentication.
If you loved this blog and are looking for more, feel free to peruse our blog section or contact us! Our team is more than happy to share what we know on Office 365. Thanks to our large array of skills, Sparkhound is able to offer more to our clients so their businesses can thrive. Get in touch with us to see how we can help your team!
Information and material in our blog posts are provided "as is" with no warranties either expressed or implied. Each post is an individual expression of our Sparkies. Should you identify any such content that is harmful, malicious, sensitive or unnecessary, please contact marketing@sparkhound.com
Share this
You May Also Like
These Related Stories
.jpg)
Manage Azure VM’s With PowerShell
-1.png)
Migrating VMware to Microsoft Azure with MVMC 2.0 Part 2
